Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
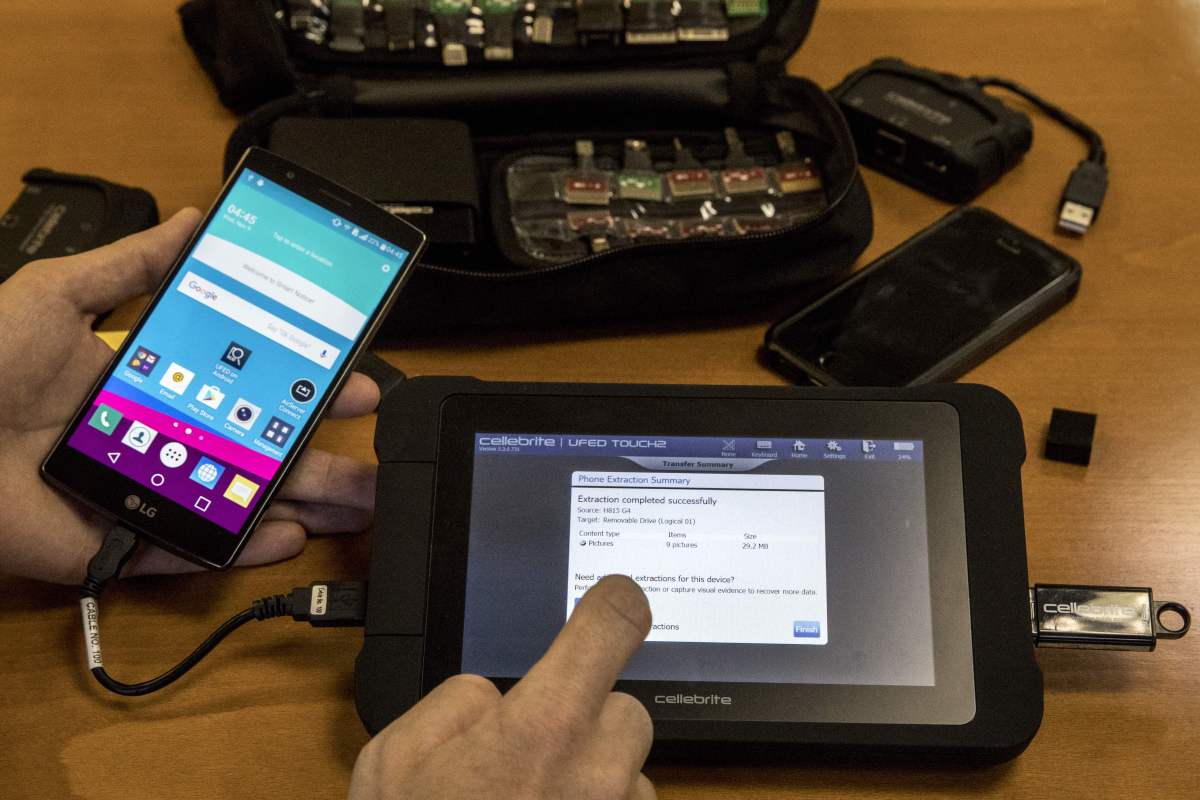
Last year, phone hacking tool maker Cellebrite made an announcement had stopped the Serbian police as clientsafter a human rights investigation against the local police and intelligence agencies he used his tools to hack the phones of a reporter and a protesterand planting spyware.
This was a rare example of Cellebrite cut the client in public following the written abuse, to mention Amnesty International technical report on his decision.
But following recent similar abuse cases in Jordan and Kenya, the Israeli-headquartered company responded by dismissing the allegations and refusing to commit to investigating them. It is not clear why Cellebrite has changed its strategy, which appears to be different from what it has done in the past.
On Tuesday, researchers from The Citizen Lab at the University of Toronto published a report alleging that the Kenyan government used Cellebrite’s tools to unlock the phone of Boniface Mwangi, a political figure and politician, while he was in police custody. In another report since January, The Citizen Lab has accused the Jordanian government of hacking the phones of dozens of protesters and activists using Cellebrite tools.
In these two studies, Citizen Laban organization that has investigated the abuses of spy programs around the world.
The researchers said that this is a “strong belief” that someone used Cellebrite’s unlocking tools on the phones in question, because the same application was previously found on VirusTotal, a malware repository, and was signed with Cellebrite’s digital certificates.
So have other researchers join the same work at Cellebrite.
“We don’t respond to speculation and encourage any organization with genuine, evidence-based concerns to contact us directly so we can take action,” Victor Cooper, a Cellebrite spokesperson, told TechCrunch in an email.
When asked why Cellebrite is acting differently in the case of Serbia, Cooper said “the two cannot be compared,” adding, “high reliance is not direct evidence.”
Cooper did not respond to several follow-up emails asking if Cellebrite would investigate The Citizen Lab’s latest report, and if there is any difference to its story in Serbia.
Do you have information about Cellebrite, or similar companies? From a non-working device, you can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, or via Telegram, Keybase and Wire @lorenzofb, or on email.
During its investigations in Kenya and Jordan, The Citizen Lab reached out to Cellebrite before publishing the reports to give the company the right to respond.
In response to Jordan’s report, Cellebrite he said that “Any legitimate use of our devices in violation of human rights or local laws will result in immediate disability,” but he did not commit to investigating the case and declined to disclose customer details.
For the Kenyan report, however, Cellebrite acknowledged that it received The Citizen Lab’s research but did not respond, according to John Scott-Railton, one of The Citizen Lab’s researchers who worked on Cellebrite’s research.
“We are urging Cellebrite to release the process they used to approve the sale to the Kenyan authorities, and disclose how many licenses were revoked in the past,” Scott-Railton told TechCrunch. “If Cellebrite is serious about their commitment to hard work, they should have no problem explaining it to the public.”
Following previous reports of abuse, Cellebrite, which what to say having more than 7,000 legal clients worldwide, cutting relationships and Bangladesh and Myanmaralso Russia and Belarus in 2021. Cellebrite previously said they stopped selling to Hong Kong and China to comply with US government regulations restricting the export of complex technologies. Freedom activists in Hong Kong he was guilty authorities are using Cellebrite to unlock the phones of the accused.